Tenants topology
Deployment steps
Create central and institutional tenants
To perform multi tenancy consortia setup lets create 3 tenants with ids: consortium, university, college
Tenant creation
For tenants creation the standard okapi tenant creating endpoint should be used: POST /_/proxy/tenants
We need to create new host with UI only for the central tenant.
Only single host need to be deployed
Consortium users will use only the central tenant DNS host for all operations, if users need to apply operations from the context of another institutional tenant - they can switch active affiliation in the header.
Enable modules on tenants
We should follow the standard procedure of enabling tenants from install.json and enable all desired modules except one UI module folio_consortia-settings that should be enabled only in the consortium central tenant
Differences between central and institutional tenants
Module folio_consortia-settings should be enabled only in consortium central tenant
Configure tenants
- Reference data & sample data should NOT be created on both central and institutional tenants.
Existing settings in a tenant cannot be shared via Consortium Manager. Settings have to be created via Consortium Manager to be shareable.
- Reset password link, SMTP for sending emails should be configured on all tenants. Separate admin users in each tenant can be created to apply all this configuration.
Create admin user in the central tenant
For Consortia setup it is required to create admin user in the central consortium tenant. For other tenants shadow admin users with required set of permissions will be created automatically during Configure consortium tenants step.
This admin user should contain all existing permissions that admin users currently have for our common envs plus 2 additional:
- consortia.consortium.item.post
- consortia.tenants.item.post
Endpoint to create admin user
Configure consortium tenants
Tenant context
Create consortium record
Validation requirements:
- Only 1 consortium record should exist across cluster. adding more is prohibited
Request to create consortium record:
POST /consortia HTTP/1.1
X-Okapi-Tenant: consortium
X-Okapi-Token: <JWT>
Content-Type: application/json
{
"id": "a617d446-4c00-4f8f-bcd4-5beacbccef67",
"name": "Mobius"
}
Create consortium tenants
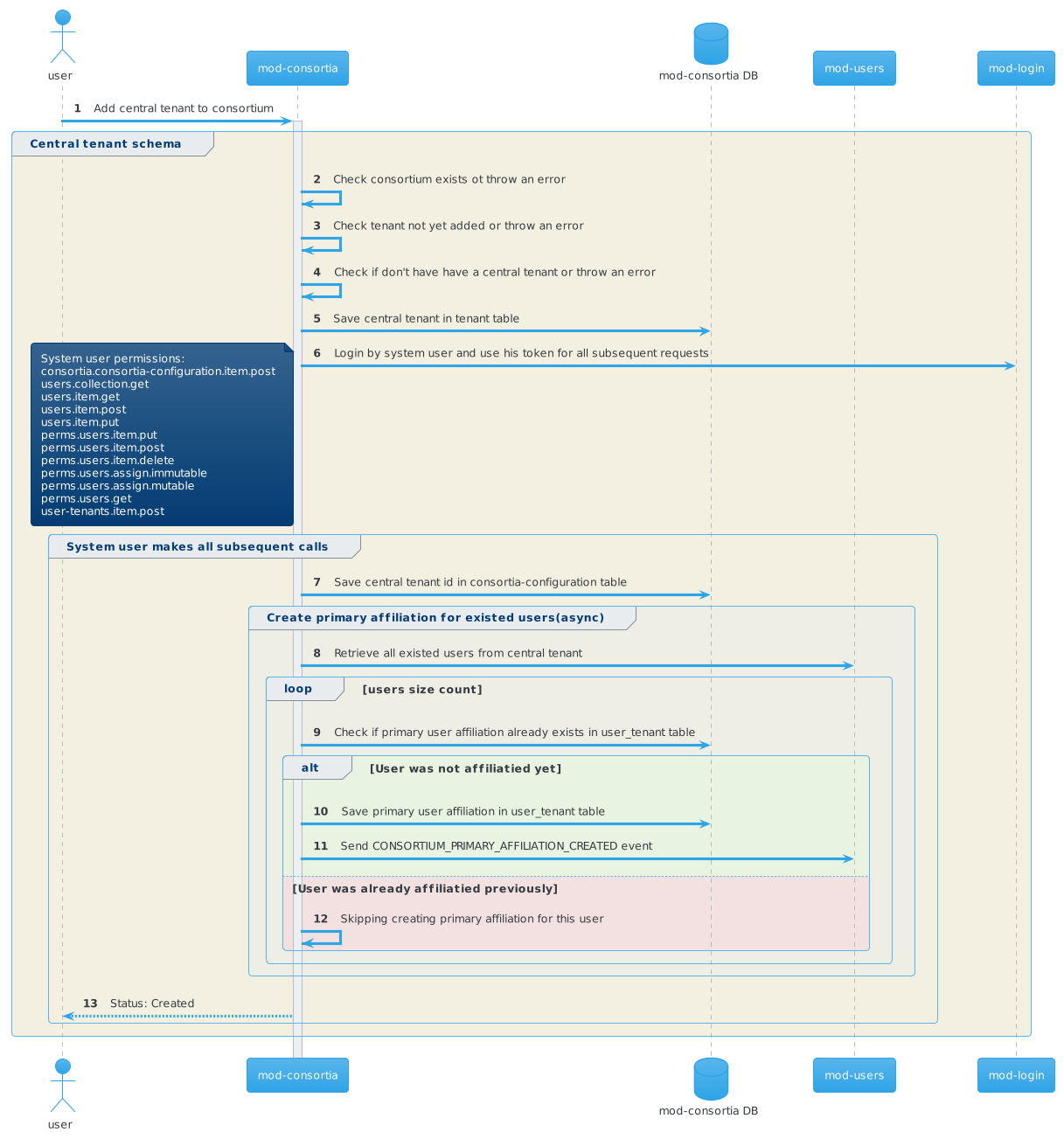
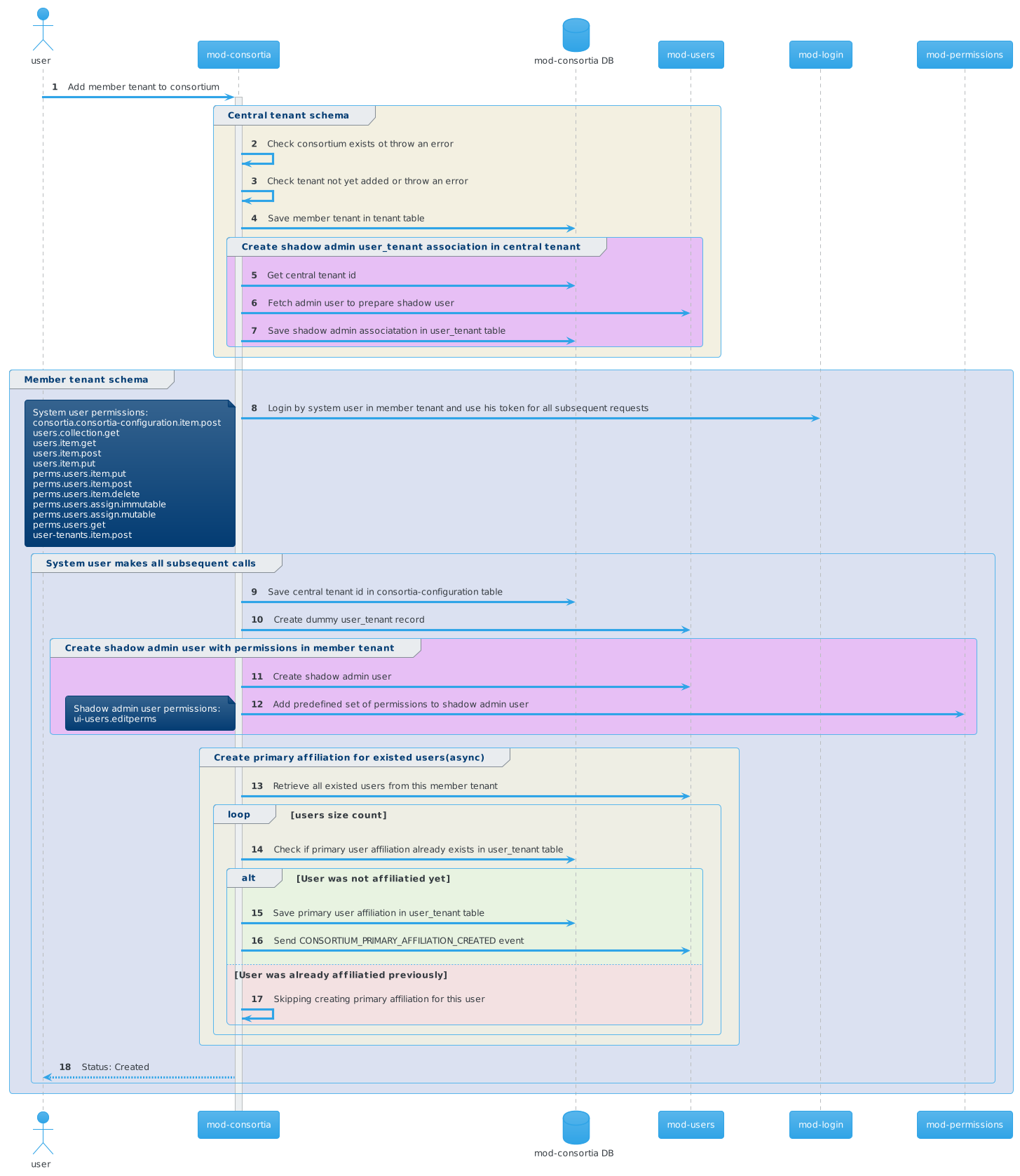
Actions performed under the hood of invoiking POST /consortia/{consortiumId}/tenants:
- Store central tenant id in the consortia_settings table of the desired tenant
- Perform primary affiliation creating for all existing users asynchronously
- Invoke /user-tenant to store dummy user
Validation rules:
- Consortium record should be created before adding tenant
- Name and code fields should be unique
- Name min length - 2, max length - 150
- Code min length - 3, max length - 3, regex pattern - '^[a-zA-Z0-9]*$'
- Tenant should not be existed already
- Central tenant should be added firstly
- Adding tenant when some another tenant has setupStatus = "IN_PROGRESS" is forbidden
Add central tenant to the consortium
Request to create central consortium tenant:
POST /consortia/a617d446-4c00-4f8f-bcd4-5beacbccef67/tenants HTTP/1.1
X-Okapi-Tenant: consortium
X-Okapi-Token: <JWT>
Content-Type: application/json
{
"id": "consortium",
"name": "Central office",
"code": "MCO",
"isCentral": true
}
Add institutional tenants to the consortium
New request param adminUserId added
Pay attenation that new request parameter adminUserId has beed added. It used to create shadow admin user in the desired teanant with predefined set of permissions.
It should be adminUserId for admin user from the central Tenant
Request to create University tenant:
POST /consortia/a617d446-4c00-4f8f-bcd4-5beacbccef67/tenants?adminUserId=b20c4397-ad56-479f-891a-30a5a471f24b HTTP/1.1
X-Okapi-Tenant: consortium
X-Okapi-Token: <JWT>
Content-Type: application/json
{
"id": "university",
"name": "University",
"code": "UNI",
"isCentral": false
}
Request to create College tenant:
POST /consortia/a617d446-4c00-4f8f-bcd4-5beacbccef67/tenants?adminUserId=b20c4397-ad56-479f-891a-30a5a471f24b HTTP/1.1
X-Okapi-Tenant: consortium
X-Okapi-Token: <JWT>
Content-Type: application/json
{
"id": "college",
"name": "College",
"code": "COL",
"isCentral": false
}
Order to add tenants to the consortium
Sequential order to add tenants to the consortium should be used, because under the hood we are making operations to create users in other tenants and simultaneously have an async operation to migrate existing users in current tenant.
Firstly, an automation job should create a central tenant and after this - all member tenants.
To control the tenant setup state we have a field 'setupStatus' in tenant response body with allowed values: "IN_PROGRESS", "COMPLETED", "COMPLETED_WITH_ERRORS", "FAILED".
Automation deployment job should make polling of GET /consortia/{{consortiumId}}/tenants/{{tenantId}} endpoint until COMPLETED or COMPLETED_WITH_ERRORS status.
Poll interval can be chosen as 10 sec for example.
mod-consortia prevents adding new tenant when some tenant in DB has setupStatus with "IN_PROGRESS" value.
Here is description of all possible statuses:
| Status | Description |
|---|---|
| IN_PROGRESS | Adding tenant to the consortium is in progress, new POST requests to add another tenants is prohibited |
| COMPLETED | Adding tenant is completed, can start adding next tenant |
| COMPLETED_WITH_ERRORS | Tenant has been added, but not all existing users have been affiliated though the mod-consortia pipeline, pipeline can continue adding another tenants. To repeat the process of syncing primary affiliations for existing users /sync-primary-affiliations can be invoked. |
| FAILED | Some unexpected error occurred, the tenant has not been added to the consortium or not all existing users have been affiliated though the mod-consortia pipeline. The preferred way here is to stop executing automation pipeline and investigate reasons for these errors via logs |
User type is required in ECS mode
On some of the customers it is possible to have more than 1.3 million of patron users, ECS does not need to process all of them through a consortium pipeline, because patron users can not and should not login to consortia.
So 'type' field for user is required now in ECS mode, for non ECS it is optional.
This change brings 2 benefits:
- General performance of ECS increases because ECS logic will work with thousands of staff/system users instead of millions of patron users
- A clear way to distinguish user types in Folio appears
Possible user types:
| № | User type | Description | Processed by consortia pipeline? |
|---|---|---|---|
| 1 | staff | Regular staff user | Yes |
| 2 | patron | Regular parton user | No |
| 3 | system | User created by internal modules usage | Yes |
| 4 | shadow | Shadow user created when adding affiliation to the desired tenant | No (kafka messages will be send only for real users, but not for shadow) |
How to deal with existing users
What is going on during this process of migrating existing users?
When adding a tenant to the consortium, the process of migrating existing users through the consortia pipeline begins within the scope of each:
- Primary affiliation, and Affiliation in the central tenant (if the user is from a member tenant), with shadow users created.
- The 'user-tenants' table in 'mod-users' is populated in the central tenant, which enables existing users to log in to ECS.
In conclusion, users processed by the consortia pipeline can log in, and affiliations will be manageable in ECS mode.
When to migrate existing users, before or after enabling ECS mode?
Before enabling ECS mode
The process of migrating existing users has been added to handle certain system or admin users through the ECS pipeline. This process is also triggered when ECS mode is enabled on a tenant that already has users with a populated 'type' field.
The query used to fetch existing users, as used by 'mod-consortia,' is as follows: (cql.allRecords=1 NOT type="patron" NOT type="dcb" NOT type="shadow"). With this query, all users without a populated 'type' field or with a 'type' that does not equal 'patron' or 'dcb' will be migrated.
One important point to consider is that if, for example, 1.5 million patron users were created without populating the 'type' field as 'patron' when ECS was not enabled, all 1.5 million users will be migrated. This behavior is not desired because the validation of the 'type' as a required field is only enabled when ECS mode is enabled, and ECS should skip processing these users in the pipeline.
After enabling ECS mode
If we have a choice, it's preferable to enable ECS mode for the tenant and then begin creating/migrating users. These users will be processed by 'mod-consortia' via Kafka domain events sent by 'mod-users.'
In this scenario, users cannot be created without populating the 'type' field because validation is enabled in ECS mode. For some customers, we may have more than 1.5 million patron users and only a couple of thousand staff users. In this case, we can ensure that 'mod-consortia' will process only these thousands of staff users and exclude the millions of patrons.
In conclusion, it's better to migrate existing users after enabling ECS mode for the tenant.
Do we need to adjust our existing admin users to populate type='staff'
Let's begin with system users. All repositories have been updated to create new system users with the type 'system,' and a migration script has been written in 'mod-users' to add 'type='system'' for all existing system users.
So, for system users, no further actions are required.
For admin users, it's advisable but not mandatory. We recommend adding 'type='staff'' to avoid confusion regarding users that existed without a populated 'type' field in ECS mode, where this type field is required.
Additionally, some new features, such as filtering by user type in the Users App, will not consider users without a 'type' value.
However, even if 'type' is not populated for admin users, 'mod-consortia' will still select such users and process them through the ECS pipeline during the 'migrate existing users' process when adding the tenant to the consortium. This process includes users without a 'type' populated.
In conclusion, no action is needed for 'system' users, but for common admin users, it's advisable to add 'type='staff''.
BE Modules modified for supporting consortia functionality
Thunderjet team
| № | Module | Changes made | Hosting changes |
|---|---|---|---|
| 1 | mod-consortia |
| Make sure that password for consortia system user populated via this env variable: SYSTEM_USER_PASSWORD, OKAPI_URL also should be populated. The full list of env variables is presented in the Readme: https://github.com/folio-org/mod-consortia#environment-variables |
| 2 | mod-users |
| - |
| 3 | mod-users-bl |
| - |
| 4 | mod-login |
| - |
| 5 | mod-authtoken |
| System param(declared in JAVA_OPTS) should be added: -Dallow.cross.tenant.requests=true RANCHER-903 - Getting issue details... STATUS |
Firebird team
| № | Module | Changes made | Hosting changes |
|---|---|---|---|
| 1 | mod-oai-pmh |
| - |
| 2 | edge-oai-pmh |
| permissions + users, To be defined |
| 3 | mod-data-export |
| - |
Folijet team
| № | Module | Changes made | Hosting changes |
|---|---|---|---|
| 1 | mod-inventory |
| - |
| 2 | mod-inventory-storage |
| - |
| 3 | mod-source-record-manager |
| - |
| 4 | mod-source-record-storage |
| - |
Spitfire team
| № | Module | Changes made | Hosting changes |
|---|---|---|---|
| 1 | mod-search |
| Tenant paramenter centralTenantId should be added(during tenant enabling) RANCHER-898 - Getting issue details... STATUS |
| 2 | mod-entities-links |
| - |
Volaris team
| № | Module | Changes made | Hosting changes |
|---|---|---|---|
| 1 | edge-patron | Provide a consortia-level access point/mechanism for retrieving patron data | - |
| 2 | edge-common | Support Consortium Authentication & Routing | - |
Issues found during consortia env setup
| № | Issue description | Related tickets |
|---|---|---|
| 1 | Simaultainious adding tenants to consortia can cause concurrent issues | MODCON-73 - Getting issue details... STATUS RANCHER-893 - Getting issue details... STATUS |